RECORDS MANAGEMENT INFORMATION SYSTEMS
Shift From Unstructured To Structured Documents!
DSI streamlines filing and document retrieval practices through our innovative records management system in Albuquerque . Paper files take up valuable office space while decreasing your employees’ productivity through extensive filing and document retrieval. PDFs, emails, and other digital documents and records become lost or inaccessible due to being stored on someone else’s hard drive.
By implementing DSI’s records information management systems, you’ll increase productivity and secure sensitive information while saving valuable time and money through innovative processes.

RECORDS MANAGEMENT SYSTEMS
DOCUMENT MANAGEMENT CHALLENGES DSI SOLVES
Disorganized Document Storage
Inefficient Workflows
Security Concerns
Digital Transformation Difficulty
Integration Challenges
Scalability Constraints
High Document Volumes
Limited Visibility & Control
Is Your Critical Business Information Trapped In A Hardcopy Format, Stuck In Someone’s Email, Or Inaccessible From A Local Server?
DID YOU KNOW?
– FinancesOnline
– Business.com
– Square 9
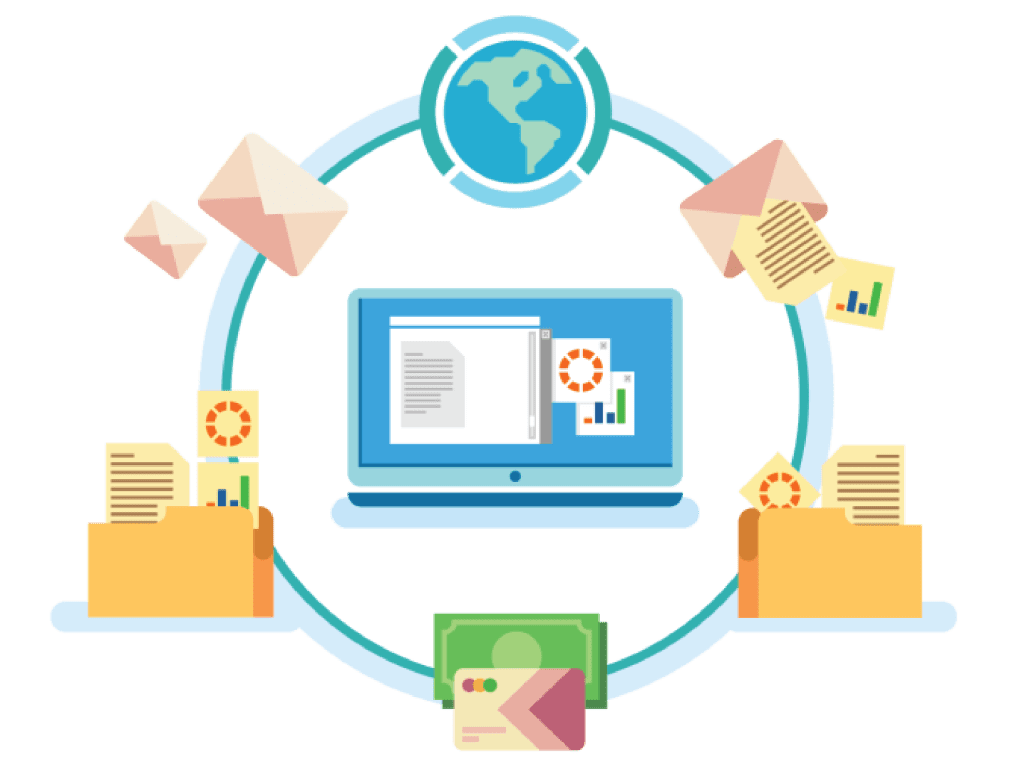
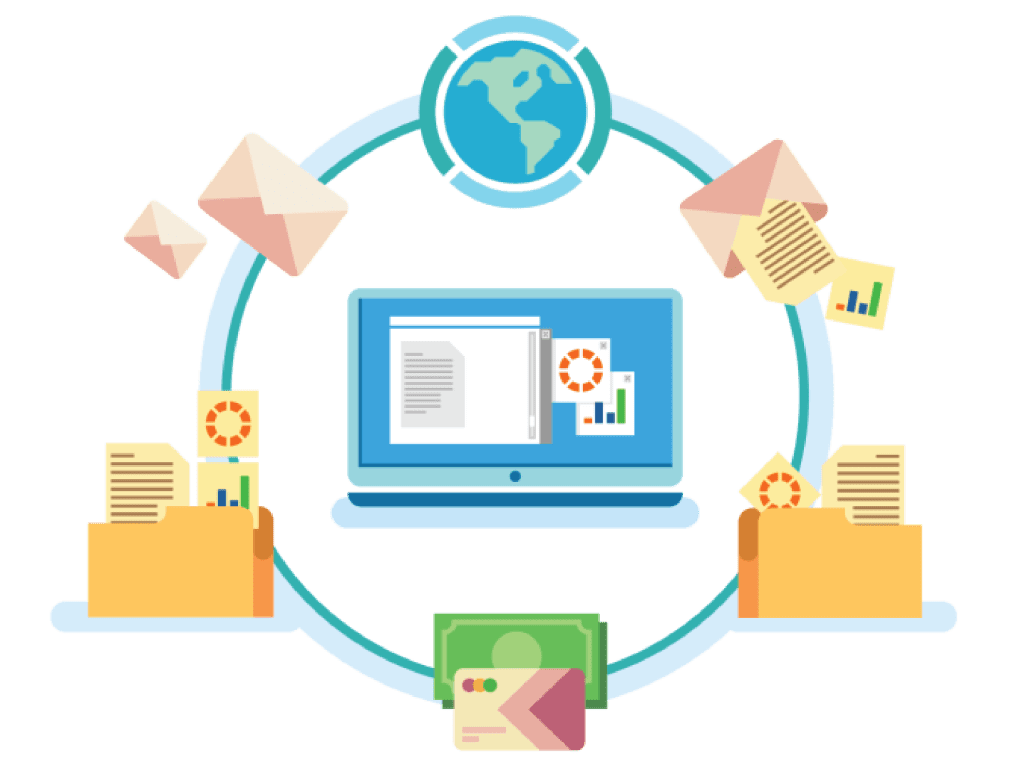
WHAT IS ELECTRONIC DOCUMENT AND RECORD MANAGEMENT SYSTEM (EDRMS)?
We transform your paper and digital files into a collaborative digital environment so your company can find, share, collaborate, and better secure information.
EDRMS stands for electronic document and records management system. This content management software application saves, organizes, and secures all your files into a searchable database. Its permission-based retrieval system ensures only those with authorization can access specific files.
EDRMS centralizes all your files, making these documents and records easy to find and access. Your company’s sensitive information remains safe through established permissions and security features, while data logs and trails help you track who’s accessing those files
GET ORGANIZED WITH EASY-TO-USE SECURED EDRMS SYSTEMS
DSI partners with Square 9 to provide EDRMS software and support. We are dedicated to delivering large and small businesses the necessary solutions to keep their documents and records secured, searchable, and easy to file. When you invest in our EDRMS systems, you receive these benefits:


Save Time And Money
Hassle-Free Seamless Integration
Our range of document management software includes offerings from leading industry partners, who provide cutting-edge technology that enables efficient filing, searching, retrieving, and sharing of documents.
Accounts Payable
EDRMS provides invaluable tools for quickly completing the Three-Way Match and additional transaction research functions.
Accounts Receivable
File searching and automated email allow you to resolve any disputed transaction quickly, so your payments keep flowing in.
Human Resources
By managing HR records, you can rest assured employee data is secure yet easily accessible in the event of a payroll review or audit.
Contract Management
Organize and categorize your agreements in a meaningful way and then launch them to Microsoft Word for editing or printing.


Needs assessment and recommendations


Structure to organize your documents
Turnkey solutions specific to your organization
Backup and disaster recovery support
Paper to digital strategy


Real-time access to critical information
Flexible collaboration


On-premise or cloud solutions


Maximum security protection
Professional installation and support


Extensive staff training


Multiple brand solutions
DSI’S SUITE OF PRODUCTS AND SERVICES
As our business grew, we realized New Mexico’s and El Paso’s businesses needed more than essential office equipment. That’s why we expanded our products and services to cover almost every need local offices require in today’s world.
Network Firewall Security
BOOST FILE PROTECTIONS WITH NETWORK FIREWALL SECURITY SOLUTIONS
DSI offers network firewall security as a defense against network intrusions. Network firewalls protect your private network, especially intranets, from being accessed by unauthorized users and entities. If your business is linked to the internet, let us show you how our network firewall security products can safeguard your business’s and clients’ information.
Video Security Systems
INCREASE SURVEILLANCE WITH BUSINESS SECURITY CAMERA INSTALLATIONS
As a business owner, you know how vital it is to protect and secure all your assets. That’s why DSI provides solutions covering your digital and physical spaces.
Our business security camera systems do more than deter intruders. Our camera systems help you manage your operations while saving you money. Here are some of the capabilities that come with our business security camera systems installations:


- Visitor vetting
- Foot traffic analytics
- Operations management
- Safety analytics
- Real-time emergency data
- Workplace safety
Unified Communications VoIP Phone Systems
MODERNIZE COMMUNICATIONS WITH ADVANCED VOIP SYSTEMS
DSI partners with Crexendo to provide VOIP phones for sale and their accompanying cloud-based systems. As New Mexico’s premier business phones company, we provide HD sound quality systems tailored with features landline systems lack.
Printers, Copiers and MFPs
CUSTOMIZE YOUR PRODUCTIVITY THROUGH PRINTERS FOR SALE, LEASE, AND RENT
In the past, if you wanted a high-quality printer, you needed to buy one outright. At DSI, we realized that buying printers wasn’t the only option.
Consider printer rentals for small businesses when needing additional printers for larger print jobs. Consider printer leases for small businesses when you want quality printers on a tight budget.
We also lease and sell large-format printers. Our wide-format printers produce high-quality imaging and colors with the versatility required for production and industrial printing.
CHECK OUT OUR ADDITIONAL PRODUCTS AND SERVICES
- Video wall installations
- Managed IT solutions
- Managed print services


DSI: YOUR PREMIER OFFICE TECHNOLOGY SOLUTIONS PROVIDER
DSI offers a combination of national resources with the flexibility of a local business, which lets us choose from various manufacturers’ and providers’ offerings. We serve our customers by finding the best solution to their problems rather than trying to force certain manufacturers’ equipment or providers’ services to do the job.
We train localized technical teams and staff to help our clients with the equipment and systems we offer. This is what our DSI teams can do:
- Installations
- Staff equipment and software trainings
- Troubleshooting
- Repairs
- Maintenance
- Answering questions and offering education


As a local company with 7 locations in New Mexico and an additional location in El Paso, we have the resources whenever you need us. We’re always a phone call or a short drive away to ensure your systems work smoothly.
When you choose multiple products and services through DSI, you get one monthly bill and one place to call when needing assistance. Plus, we not only know how to integrate our systems together but also know how to integrate our solutions with your existing systems.


FREE ASSESSMENT
Ready To Reinforce Your Records?
As no two businesses are the same, creating a tailored office software solution is essential for ensuring optimal operational efficiency and streamlining your daily tasks. For over 25 years, DSI has been helping businesses across New Mexico and West Texas develop office and software solutions to help companies survive and thrive. Contact us today to see how our records management system in Albuquerque can transform and safeguard your digital and paper record-keeping practices.